Your dental practice likely files claims electronically and deals with large amounts of protected health information (PHI) about your patients. As a result, your practice is defined as a “covered entity” by the Health Insurance Portability and Accountability Act (HIPAA). This means that your office must be HIPAA compliant or face corrective action and tens of thousands of dollars in fines.
The History of HIPAA
When Congress first enacted the Healthcare Insurance Portability and Accountability Act (HIPAA) in 1996, it was only intended to “improve the portability and accountability of health insurance coverage” for employees between jobs and to combat fraud and abuse in the health insurance and healthcare industry. But because this act simplified the administration of health insurance, it encouraged the digitization of patient health records, making it necessary to safeguard the security of patient data that was in a digital format.
As a result, the first HIPAA Privacy and Security rules were developed. The Privacy Rule was enforced starting in 2003, while the Security Rule began in 2005. Since 1996, Congress has expanded HIPAA rules with the enactment of the HITECH Act in 2009 and the Omnibus Rules, what has been deemed the “final” HIPAA law. Together, they monitor three types of data safeguards: administrative, physical, and technical.

Administrative safeguards had a goal of creating policies that would clearly show how the “covered entity” would comply with HIPAA.
Physical safeguards were designed to control physical access to patient data storage areas.
Technical safeguards were put in place to protect communications containing PHI when transmitted electronically over open networks.
Your dental practice must be aware of these safeguards and employ policies and tools to keep the PHI of your patients safe in all three ways.
For example, you should have administrative rules set up so that only the employees who need to access PHI as part of their jobs can do so. You should also store your data in a data center that is protected by camera systems, reinforced locks, etc.—whether that center is on or off-site. Lastly, every computer or device should be password protected and on a secure network, and your data should be encrypted to HIPAA standards.
HIPAA Violations
A serious HIPAA violation can cost your practice thousands of dollars. Violations can come not only as a result of errors at your practice, but as a result of the errors of companies you work with (defined as “business associates”). Henry Schein Practice Solutions, Inc., a leading vendor of software solutions for dental practices, was recently fined $250,000 and must comply with a 20-year consent order because they falsely advertised their software’s level of data encryption as up to HIPAA standards. This left thousands of patients vulnerable and the dentists using their software open to HIPAA violations.
The problem, however, is that the rules for HIPAA compliance can be difficult to understand, and even harder to maintain. But as OCR has ramped up the frequency and reach of their audits, it’s more important today than ever to maintain compliancy and consistently make an effort to protect the private data of your patients. Most practices make at least one of these key mistakes when it comes to maintaining HIPAA compliance. They may:
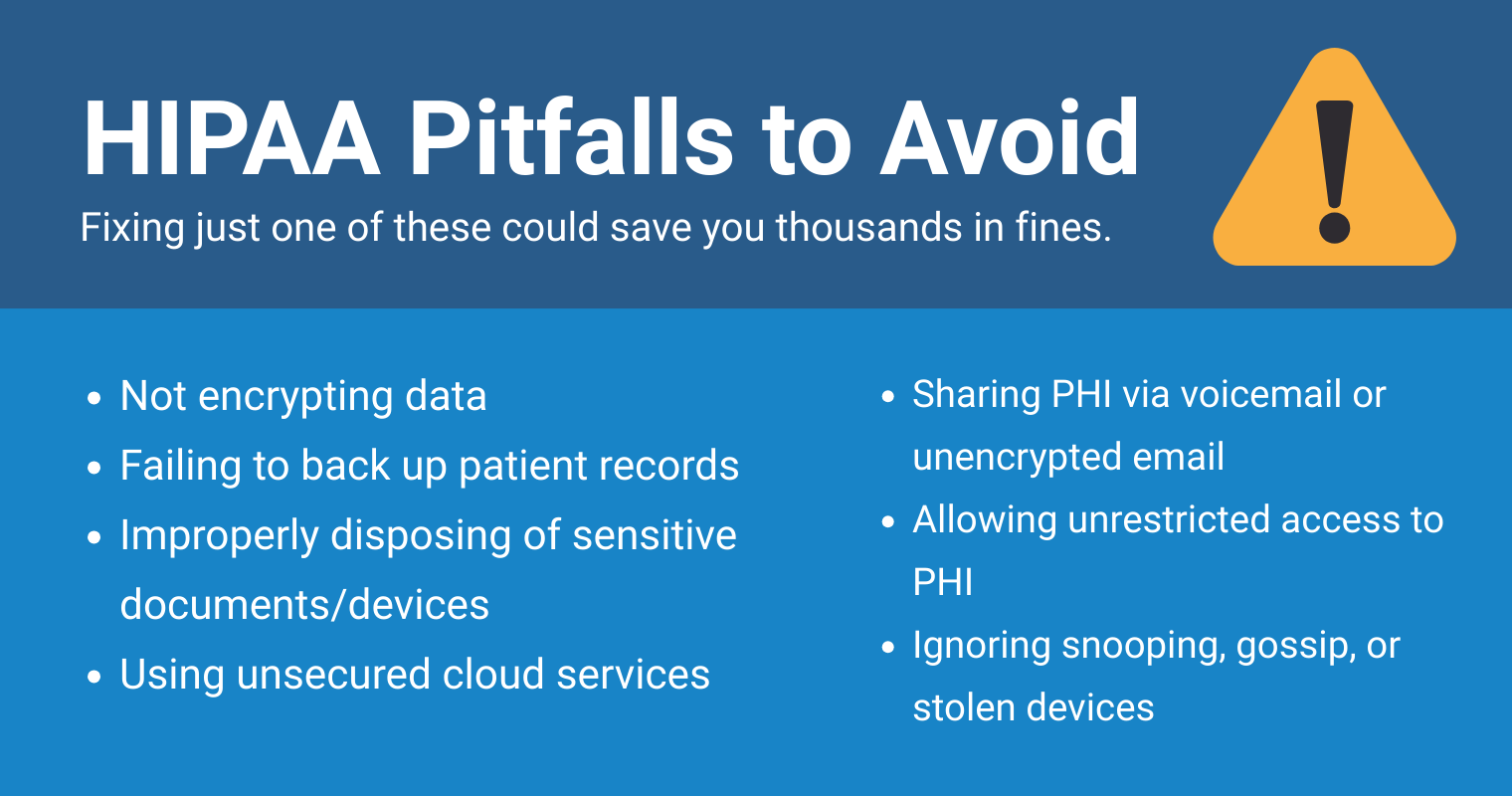
- Not encrypt their patient data
- Not backup patient data regularly
- Not properly discard of papers and devices with patient data
- Send sensitive patient information through email without encryption
- Disclose too much sensitive information over voicemail
- Use Dropbox or a similar cloud service to store and share patient data,
- Not restrict access to sensitive patient information
In addition, practices are susceptible to employee snooping or gossip about patient cases, device loss or theft, and hacking incidents.
Auditing Procedures
OCR now randomly sends out (through email) Phase I HIPAA Surveys to healthcare providers. This survey requests detailed information about your HIPAA practices and your practice’s revenue and income. It’s important to respond to this survey, so make sure to monitor your SPAM filter should it come through there.
If after this point the OCR still questions your HIPAA compliance, you will be put into a pool of potential practices to be audited. If you are selected for an audit, which is called a Phase II In-Office HIPAA Audit, you could have little to no time to prepare for a live, in-office visit from a HIPAA inspector. A Phase II Audit could last for up to 18 months, and can typically bring $10,000 to $15,000 in fines for a small dental practice.
How to Maintain Compliance
Your practice should have each computer or device and entire network system undergo a HIPAA vulnerability assessment at least once a year, though larger practices should do this assessment more often. HIPAA rules clarify this requirement.
“A thorough risk assessment/analysis [(45CFR§164.308(a)(1)(ii)(A)] for the Security Rule includes a comprehensive assessment of the internal and external networks whether wired, wireless, or cloud-hosted. In addition, the report must include a technical vulnerability assessment of all the IT assets, all electronic protected health information (ePHI), and physical and environmental controls, and operational processes (policies and procedures) of the underlying IT infrastructure across the enterprise.”
Annual HIPAA training is also required by law and will help educate your dental office employees about HIPAA requirements. Each current employee that deals with PHI must be educated about HIPAA, and each new employee that joins your practice in the future must be trained within a “reasonable” amount of time.
Your Next Step
HIPAA compliance is one of the most important factors in maintaining the value and integrity of your dental practice. Though the many rules associated with HIPAA compliance can be difficult to understand, it is necessary to take them seriously and do as much as you can to protect your clients’ personal information, especially if you are looking to sell your practice in the future. To help you determine your current level of compliancy and keep you on track in the future, we’ve developed a HIPAA and IT Security Checklist for your easy reference. Download our checklist today and assess your practice’s level of HIPAA compliance!